UNIFY AND EXTEND YOUR SECURITY STACK
Eliminate Blind Spots Revolutionize Threat Hunting
Stop reacting to fragmented data. Flecks adds the missing layer of deep endpoint interrogation to your cybersecurity ecosystem, unifying detection, hunting, investigation, and remediation into a single, proactive workflow that finds what other tools miss.
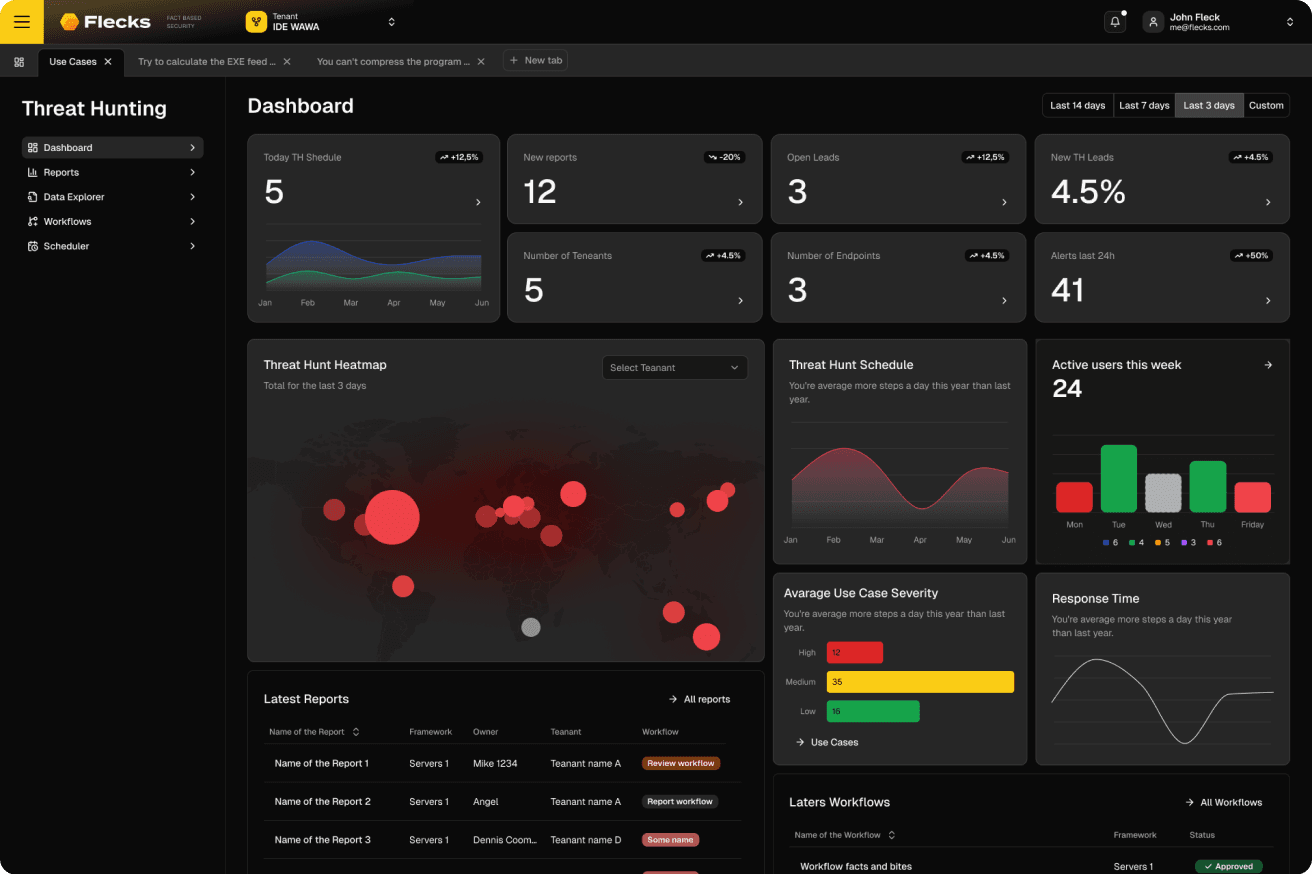
Drive Strategic Outcomes
Your security strategy must move as fast as your business. Flecks transforms reactive firefighting into proactive resilience, ensuring your infrastructure, brand, and bottom line are defended against the threats that matter most.
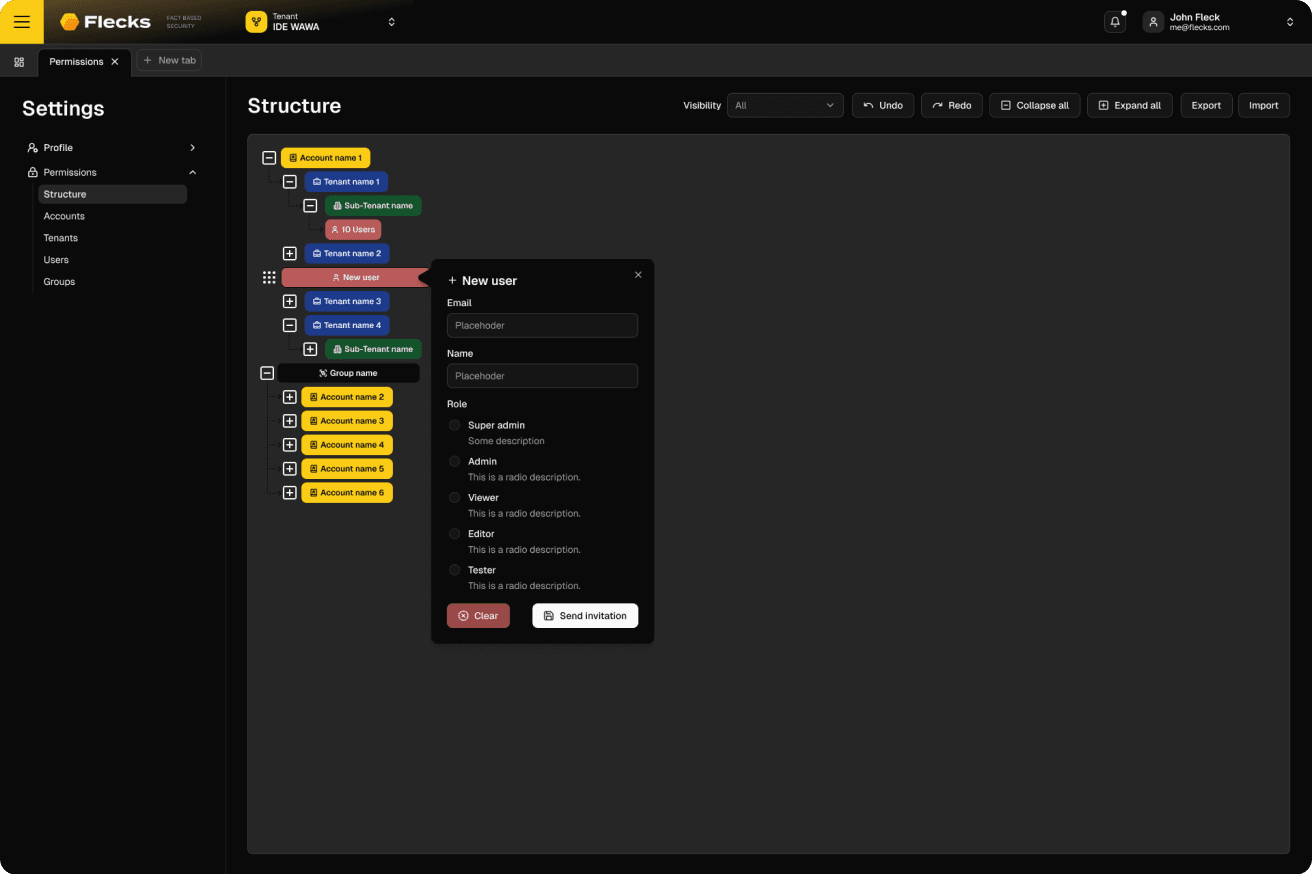
Achieve Unified Global Visibility
Security silos create blind spots, but the CISO is accountable for the entire estate. Flecks bridges the gap between decentralized teams and disparate tools, connecting global assets into a single, unified view that ensures leadership understands the true threat profile across every business unit.
Accelerate Incident Resolution
When a breach hits, time is the enemy. Flecks eliminates the fog of war by rapidly generating forensic timelines the moment a threat is suspected. Move from alert to containment in minutes and get back to business faster.
Engineer a Superior Defense
Move beyond the limitations of standard sensors and stitched-together workflows. Flecks delivers the architectural depth, automation, and unified intelligence required to operationalize a truly world-class security program.
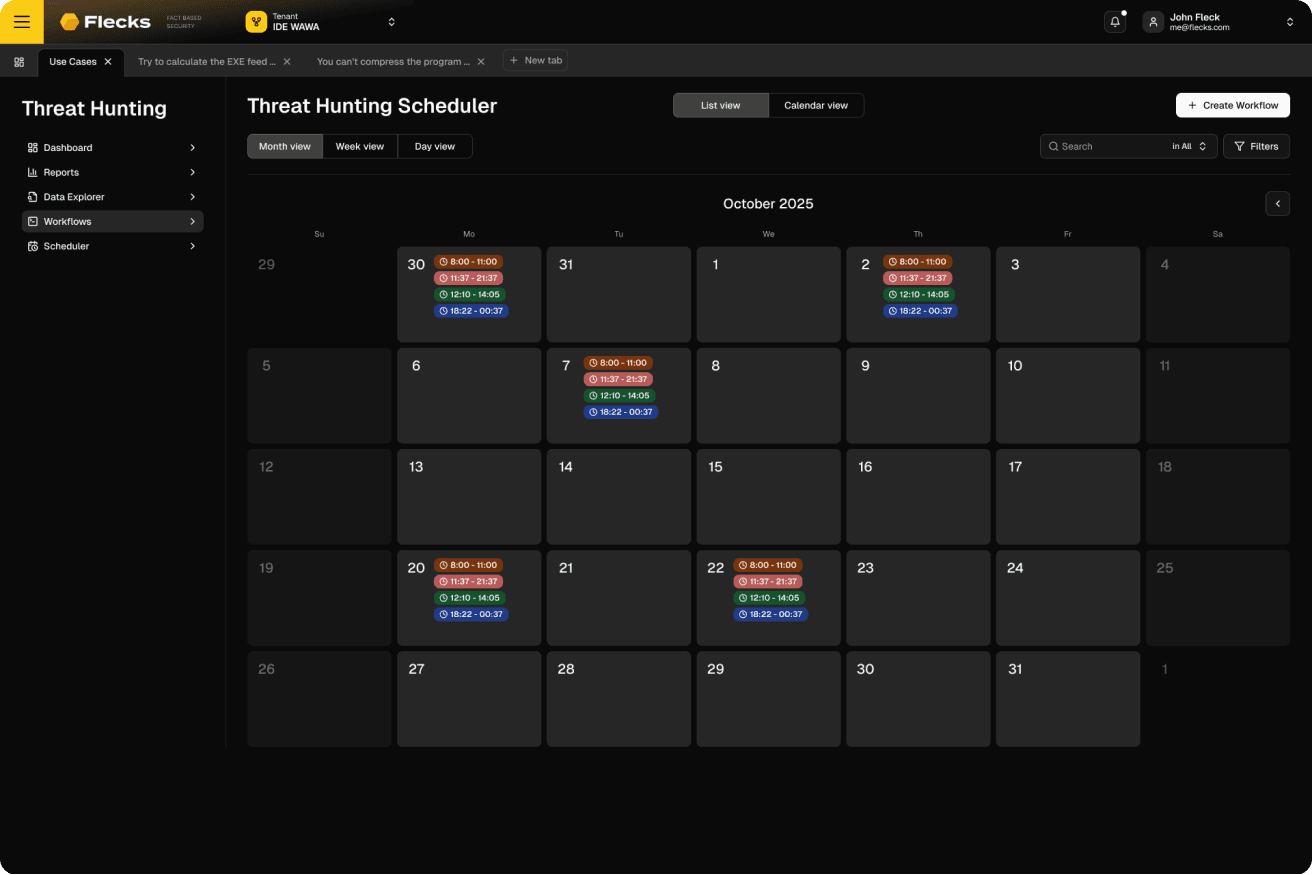
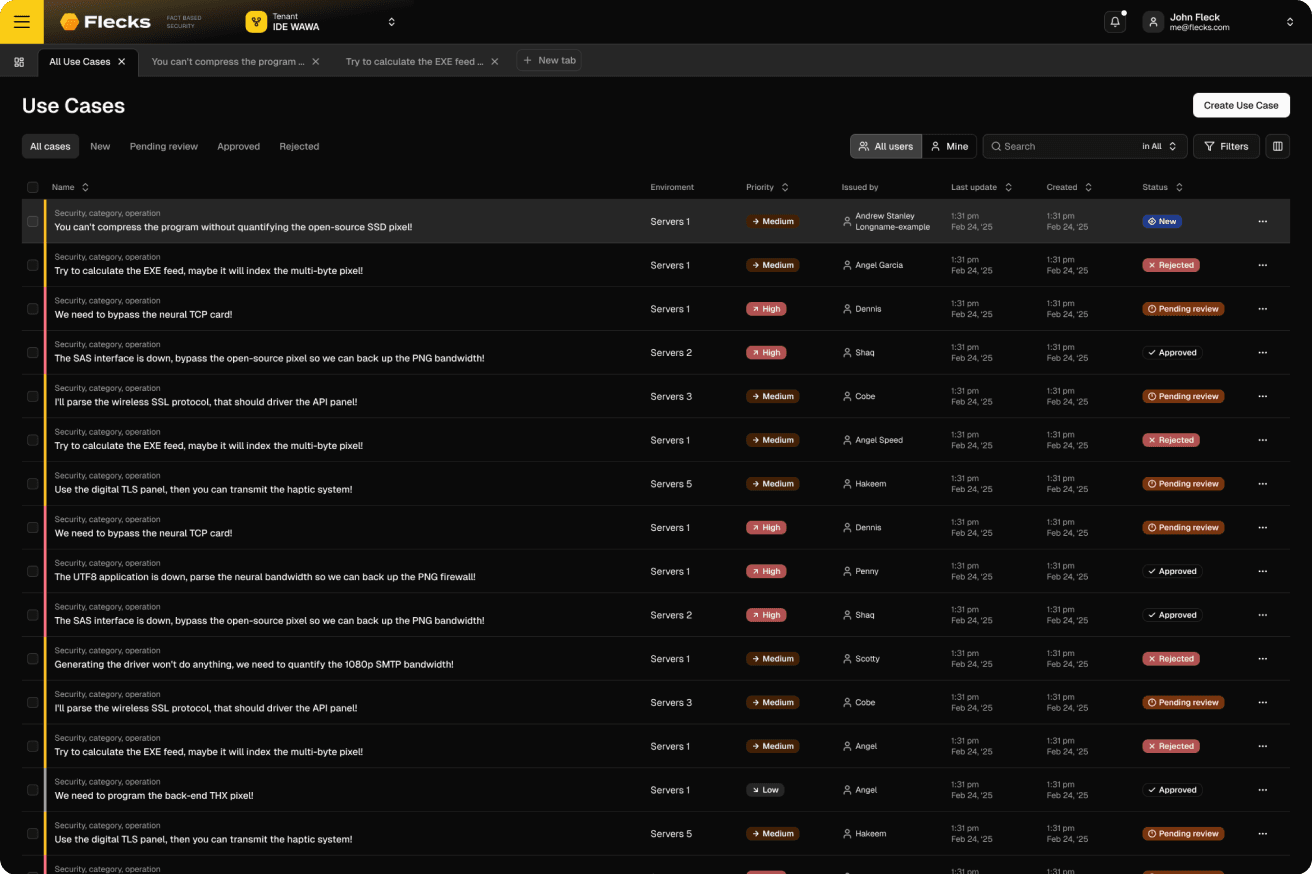
Operationalize Autonomous Threat Hunting
Transform threat hunting from ad hoc guesswork into a continuous, data-driven operation. Flecks automates the hunt lifecycle, executing expert-level logic 24/7 to uncover adversaries that slip past real-time defenses.
Accelerate DFIR Investigations
Stop burning hours jumping between tools and manually collecting evidence. Flecks unifies the entire DFIR lifecycle into one seamless, automated platform.
Unify Your Telemetry with Deep Endpoint Interrogation
See everything, not just what logs surface. Flecks fuses SIEM, EDR, cloud, and identity telemetry with Deep Endpoint Interrogation, pulling YARA, SIGMA, and rich artifacts into one view.
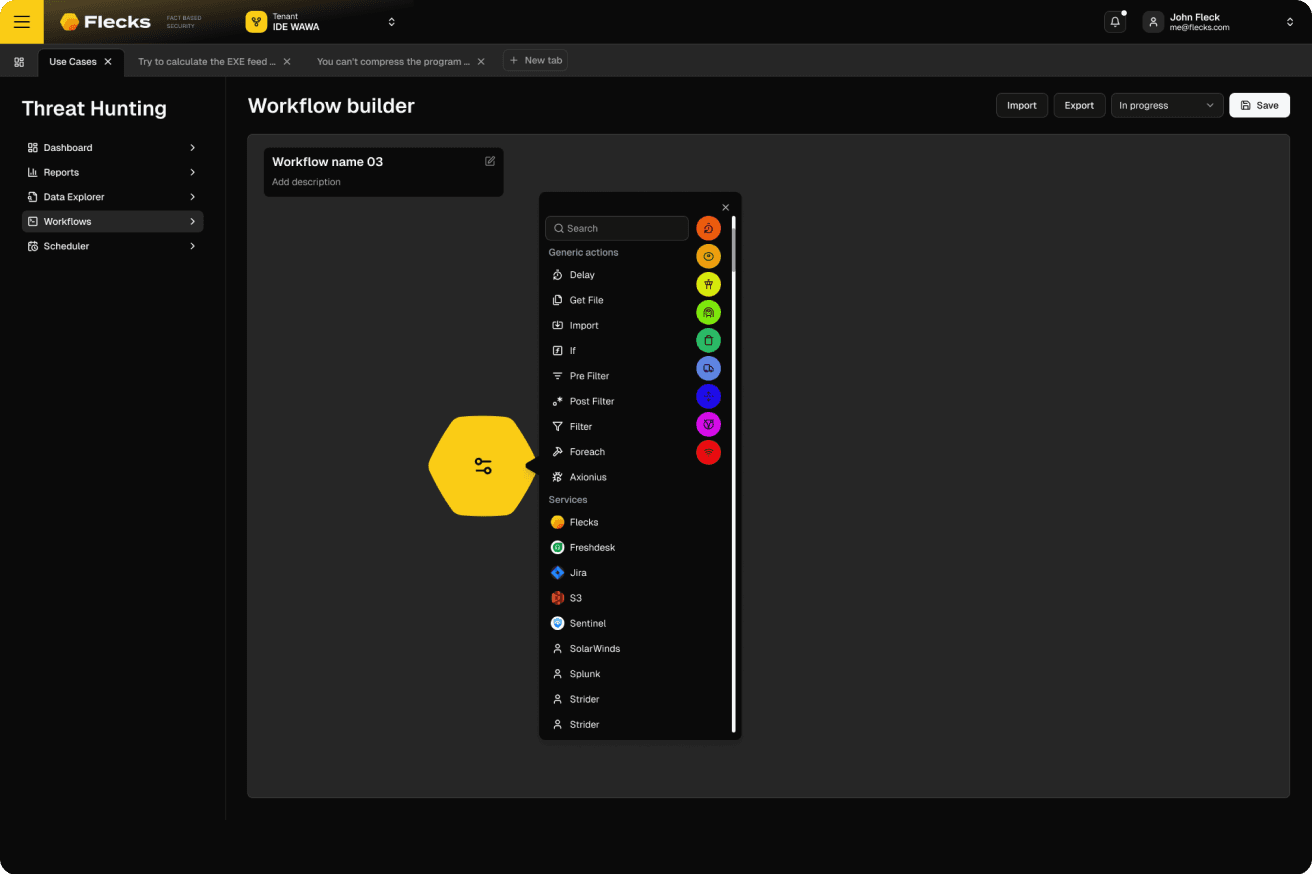
Automate Workflows with Autonomous SOAR
Flecks' autonomous SOAR engine automates enrichment, evidence gathering, and response actions so analysts stay focused on decisions, not drudgery.
Validate Vulnerabilities and Exploitation
Understand real risk, not theoretical CVSS scores. Flecks determines whether vulnerabilities are actively being exploited.
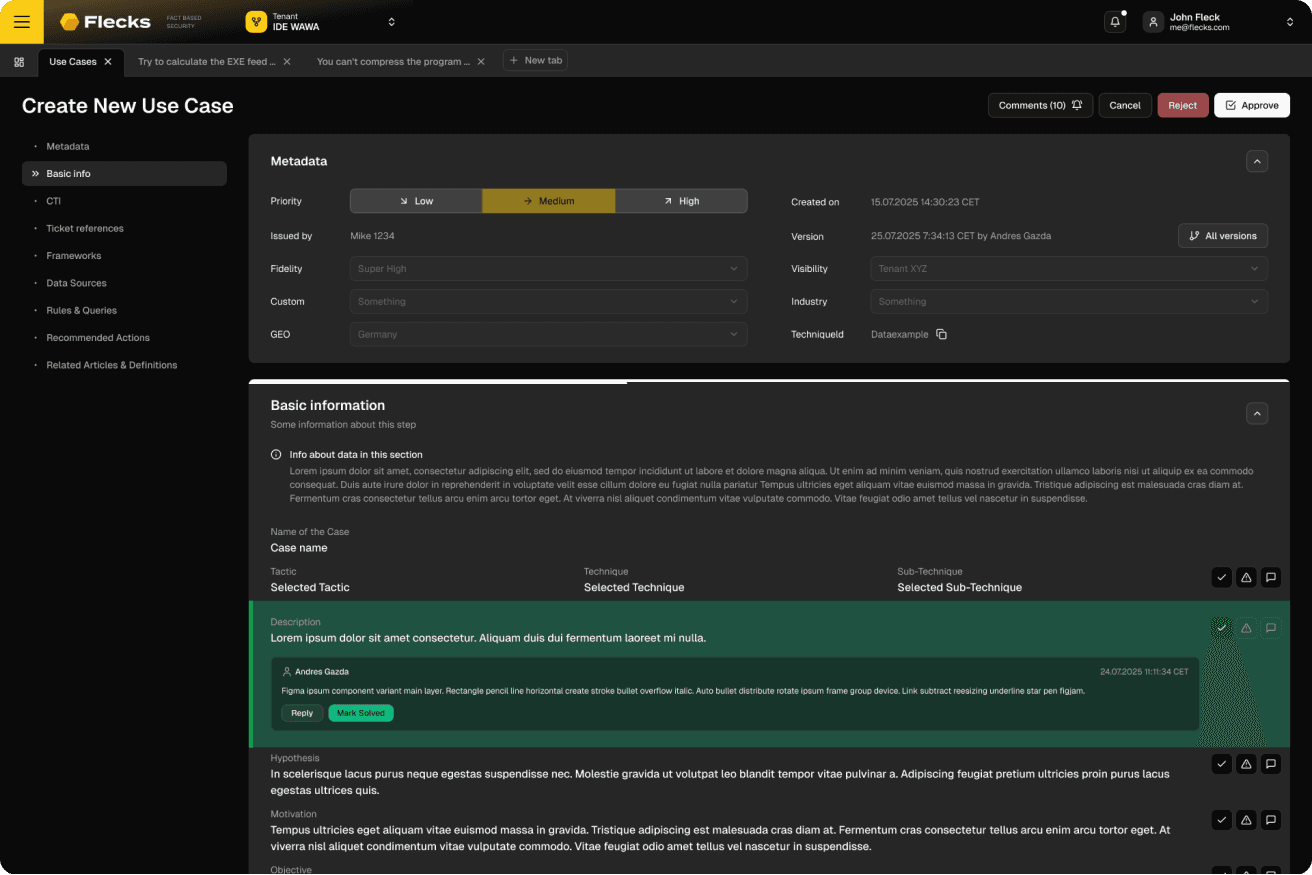
Deploy Integrated Threat Intelligence
Don't start from scratch. Flecks ships with a deep library of expert-built use cases and ready-to-run logic.